In this how to, we will learn three differents way to edit IPtables rules :
- CLI : iptables command and his config file /etc/sysconfig/iptables.
- TUI/textual interface : setup or system-config-firewall-tui
- GUI : system-config-firewall
It is not an how to about making elaborates rules with iptables, we only use iptables on a basic way.
CLI
Hot changes in iptables rules content
This method allow you to change behaviour of your iptables firewall when is running.
Read the man pages about iptables for further explanations and more sophisticated rules example.
List rules
Current running iptables's rules can be viewed with command
iptables -L
.
Example of iptables rules which allow any connections established or related, icmp requests, all local traffic and finally ssh communication :
[root@server ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT icmp -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Rules apply in order of appearance and exit if there is a match. So, if a rule that reject ssh connections is created then after another rule allowing ssh then once the reject rule is reached, the packets exit and apply reject rule but never reached accept rule.
Append a rule
This add a rule at the end of the specified chain of iptables :
[root@server ~]# iptables -A INPUT -p tcp --dport 80 -j ACCEPT [root@server ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT icmp -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh ACCEPT tcp -- anywhere anywhere tcp dpt:http Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Notice the last line in chain INPUT. There are now 5 rules in that chain.
Delete rules
To delete a rule, you must known rule's position number. Example with rule created earlier that is in fifth position :
[root@server ~]# iptables -D INPUT 5 [root@server ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT icmp -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Insert rules
Create a rule at top position:
[root@server ~]# iptables -I INPUT 1 -p tcp --dport 80 -j ACCEPT [root@server ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT tcp -- anywhere anywhere tcp dpt:http ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT icmp -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Number supplied after chain name is needed to know before which existing rule, the new rule is inserted. So, if you want to insert this rules before the third rule you as to change this number to 3.
Replace a rule
The rules about the http server is pretty wide for acceptance. Restrict a little more this rule by only allow a specific network 192.168.0.0/24 :
[root@server ~]# iptables -R INPUT 1 -p tcp -s 192.168.0.0/24 --dport 80 -j ACCEPT [root@server ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT tcp -- 192.168.0.0/24 anywhere tcp dpt:http ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT icmp -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Flush rules
To clear out iptables rules use --flush, -F option :
iptables -F <chain>
<chain> is optionnal. Without it, all chains are flushed.
Example to flush rules in OUTPUT chain :
[root@server ~]# iptables -F OUTPUT
Make changes persistant
When editing iptables rules with iptables command, if there is a reboot then changes in rules are lost.
Happily, iptables comes with two useful utilities : iptables-save and iptables-restore.
- iptables-save : print a reusable dump of current iptables rules. You have to redirect to a file like that :
[root@server ~]# iptables-save > iptables.dump [root@server ~]# cat iptables.dump # Generated by iptables-save v1.4.12 on Wed Dec 7 20:10:49 2011 *filter :INPUT DROP [45:2307] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [1571:4260654] -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT -A INPUT -p icmp -j ACCEPT -A INPUT -i lo -j ACCEPT -A INPUT -p tcp -m state --state NEW -m tcp --dport 22 -j ACCEPT COMMIT # Completed on Wed Dec 7 20:10:49 2011
- iptables-restore : restore a dump of rules made by iptables-save.
[root@server ~]# iptables-restore < iptables.dump [root@server ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT icmp -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
At each stop of service, current state of iptables rules set is saved in a file and each start the service restores this file. The file is located in :
/etc/sysconfig/iptables
for IPv4/etc/sysconfig/ip6tables
for IPv6
So, if you prefer, you can edit this file and restart the iptables service to commit the changes. The format is pretty the same than iptables command :
# Generated by iptables-save v1.4.12 on Wed Dec 7 20:22:39 2011 *filter <--------------------------------------------------------- Specify the table of the next rules :INPUT DROP [157:36334] <----------------------------------------- This is the three chain belong to filter table, then the policy of the chain :FORWARD ACCEPT [0:0] <------------------------------------------- and between brackets [<packet-counter>:<byte-counter>] numbers is for :OUTPUT ACCEPT [48876:76493439] <--------------------------------- debug/informations purpose only. Leave them at their current value. -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT <--------- A rule. -A INPUT -p icmp -j ACCEPT <-------------------------------------- You just have to take all arguments -A INPUT -i lo -j ACCEPT <---------------------------------------- of an iptables command. -A INPUT -p tcp -m state --state NEW -m tcp --dport 22 -j ACCEPT COMMIT <---------------------------------------------------------- Needed at each end of table definition. Commit rules in that table. # Completed on Wed Dec 7 20:22:39 2011
If needed, to reset packet and byte counters, use -Z, --zero :
iptables -Z <chain> <rule_number>
It is possible to reset only reset a single rule counter. It can be useful, if you want to know how many packets were captured for a specific rule.
TUI/semi graphical
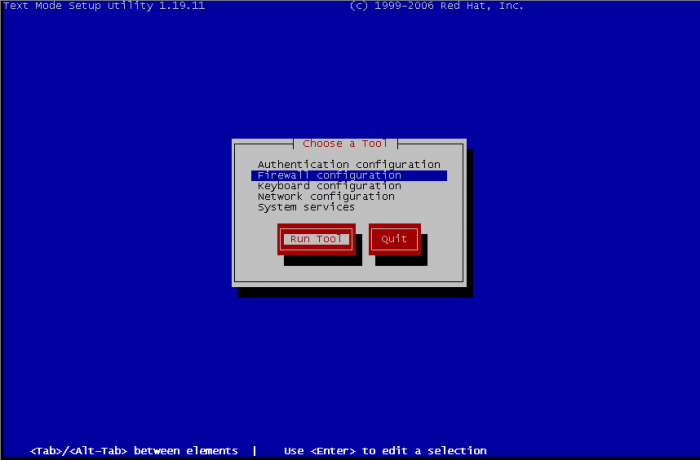
There is two ways for managing iptables rules with textual interface, by setup and system-config-firewall-tui. In the first choice you need to select firewall configuration and then edit rules, the second will bring directly to the edition of rules. So, with setup, select Firewall configuration :
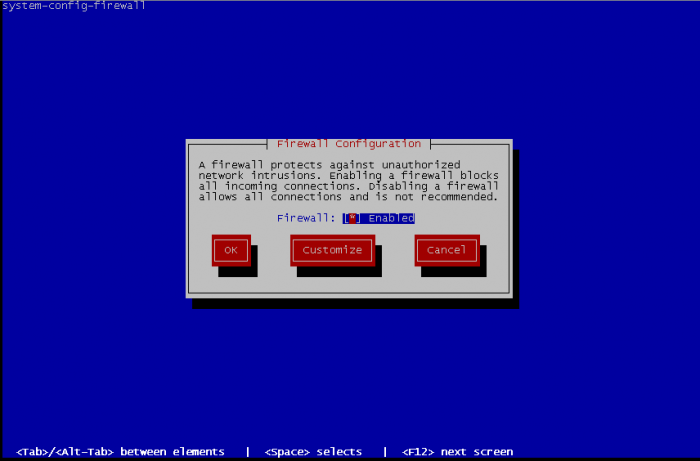
On the next screen, leave Firewall enabled or activate it if it wasn't enabled. Then we go on Customize :
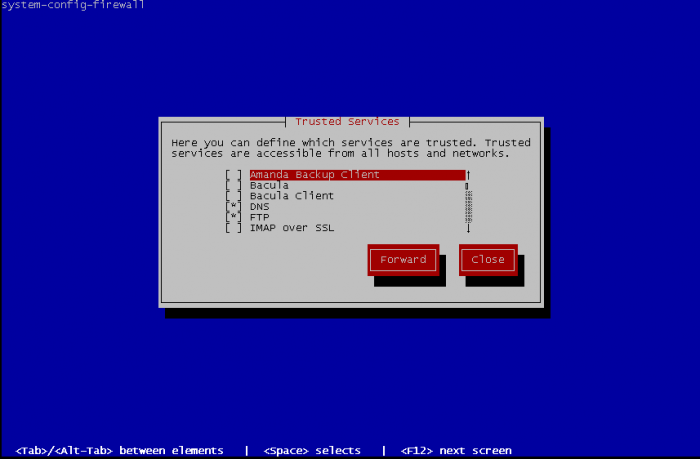
There is high chance that your service is part of the list of trusted services. This is basic activation of some standards services. Select what is needed and go Forward :
Now Edit other allowed ports :
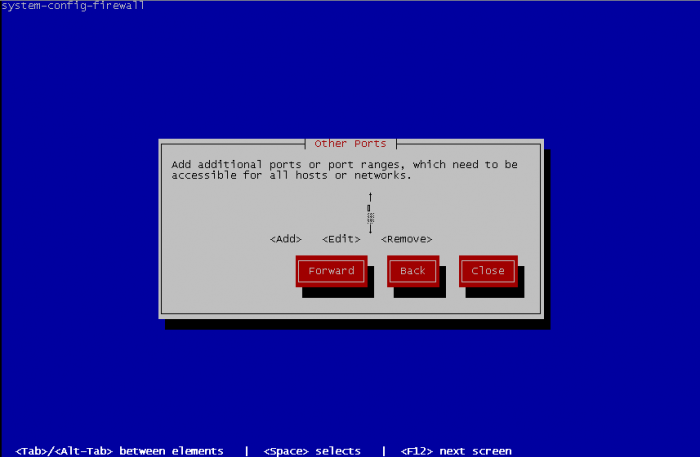
To add other ports, specify one port or a port range, and choose between tcp or udp for protocol. Port range format is beginningPort-endingPort.
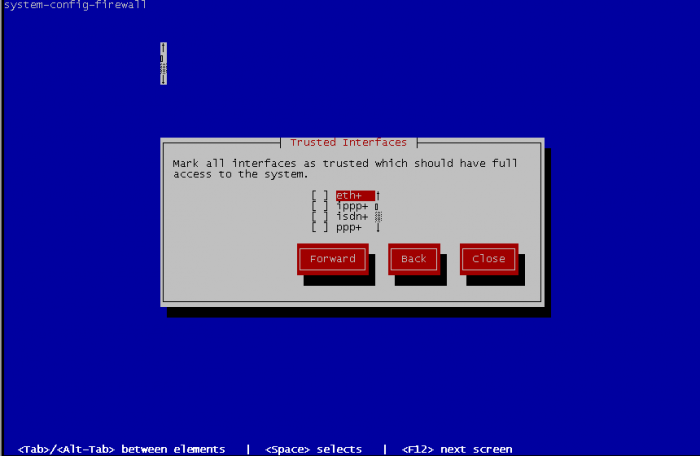
Select the trusted interfaces. These interfaces will become open face of network, all traffic will be allowed and the precedents rules will never match. So select an interface that face of a private network and never an interface that have to directly deal with internet.
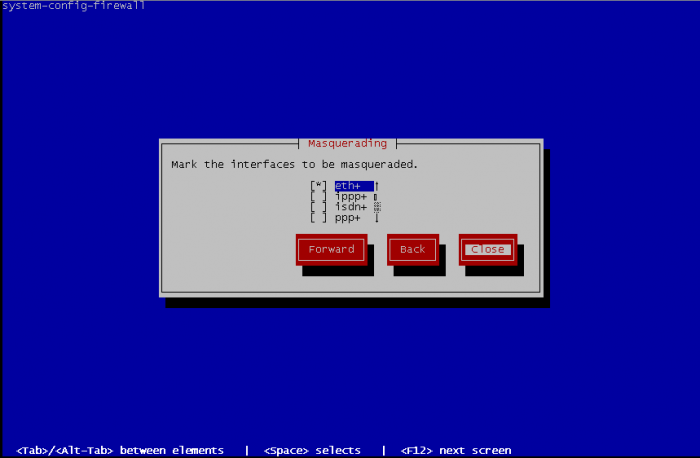
Select interfaces to be masqueraded. Masquerading is better known as NAT (Network Address Translation), it is useful by example when your Fedora computer is used as gateway to access the internet :
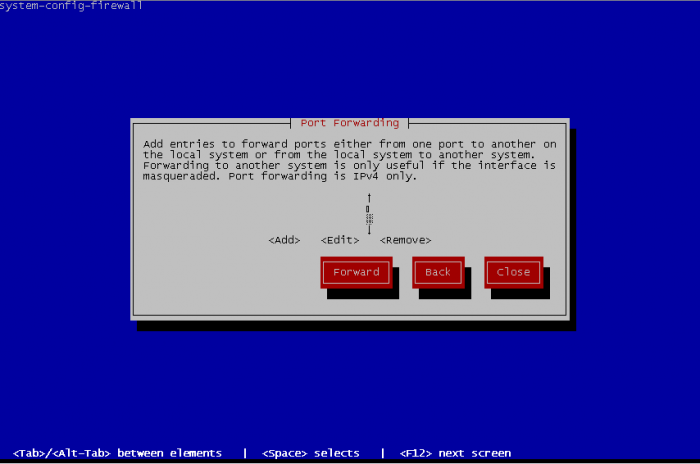
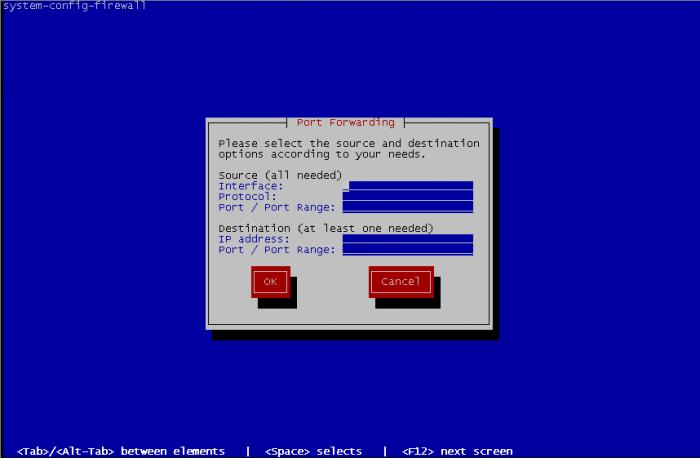
Port forwarding is also known as PAT permit to reroute traffic from a port to another port
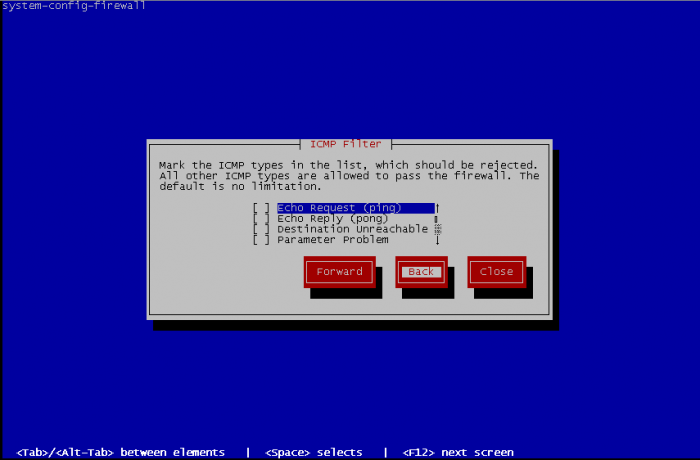
You can define ICMP behaviour of your fedora. By default, no limitations are made but you can define rules to reject ICMP traffic, define the return error to an ICMP request, etc.
Finally, you can define some custom rules. But it is needed to edit a file containing your custom rules before, with same format than the iptables file, but without specifying the table of iptables used.
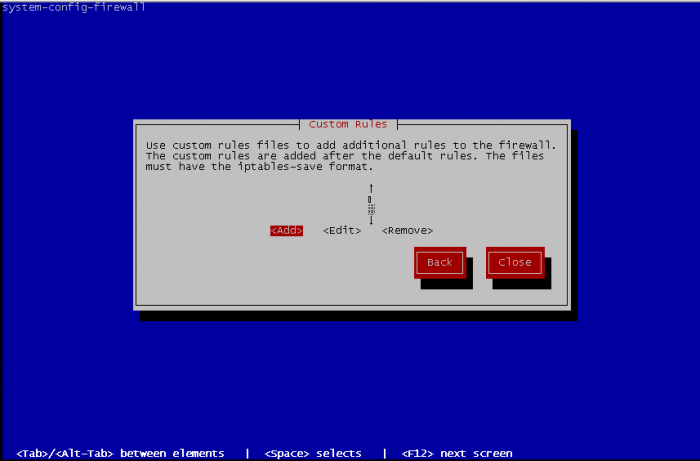
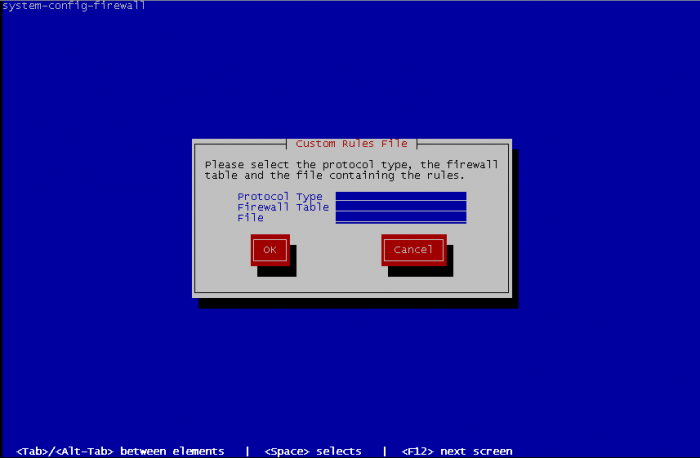
For adding custom rules you have specify the protocol between ipv4 or ipv6 and on what table add the custom rules filter, mangle or nat then the path to the file containing rules to add :
When it's done, Close the interface and this bring you at first screen of firewall configuration. Select OK and a warning message appear :
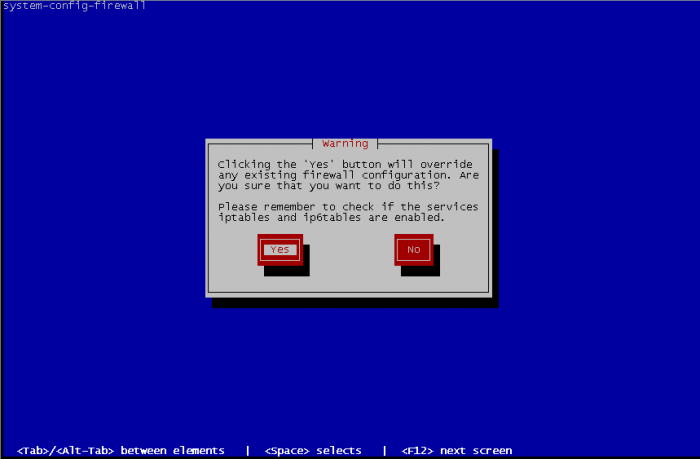
Select Yes if the configuration you made fits to you and exit interface, or No for came back to the firewall configuration screen.
GUI
Red Hat GUI configuration tool
GUI interface allow you exactly the same thing that TUI interface, but it is more friendly usable.
First time you start GUI, you have a welcome message that warning you that if you have existing manual rules then this rules will be overwritten.
Before all, you need to Enable your firewall to use Firewall Configuration utility.
Then utility warn you that you don't have any existing configuration and want you execute the wizard. Click on Start wizard:
Click on forward :
System with network access enable Firewall and System without network access disable Firewall, so select System with network access :
Beginner allow you to modify only Trusted Services, it's fine if you use only known services like ftp, dns, http, etc but don't allow you to configure customs ports range, select Expert to have full featured Firewall Configuration utility, you can change this option later in the Options menu Main windows, in User Skill Level :
Server template enable only ssh port on firewall configuration Desktop template enable additional ports for IPsec, Multicast DNS, Network Printing Client and SSH. For convenience select Desktop, and OK :
As described earlier Desktop template enable 4 services IPsec, mDNS, IPP and SSH. If you have services listed in Trusted Services section that you want to enabled, you just have to click on it, that's all. It is possible to change template by using the Options menu, in Load Default Configuration.
Other Ports allow you to edit custom rules if your service port wasn't in Trusted service. To begin, just click on Add button. Then either you choose in services list the right service or you tick User Defined and fill requested information about Port / Port Range and Protocol.
'Trusted Interfaces, Masquerading, Port Forwarding, ICMP Filter and Custom Rules have exactly the same effect than in TUI interface.
When configuration fits to you, just click on the Apply button.
Others GUI
There are others GUI available to configure iptables rules.
- [fwbuilder] : very complete gui tools to configure iptables.
- [Shorewall] : another very complete gui like fwbuilder.
- [Turtle firewall project] : web interface and integrated to webmin. Fits to basic usage of Iptables, can not handle all iptables options like fwbuilder
- [IPmenu] : console based interface that allow you all iptables functionalities.
